With the growing threat of attacks, in today’s landscape it has become increasingly important for organizations to take proactive measures. As more and more businesses rely on Kubernetes as their container orchestration platform it is crucial to have protection against ransomware.
Kubernetes offers a scalable solution for managing applications in containers. However the distributed nature of Kubernetes environments also makes them susceptible to attacks. This is where Trilio, a leading data protection software, becomes essential.
Trilio ensures the safety and integrity of your Kubernetes environment by providing protection against ransomware. It allows you to effortlessly backup and restore data minimizing downtime and preventing attackers from encrypting your files.
Don’t leave your Kubernetes environment exposed to the risks posed by ransomware. Discover how Trilio’s robust data protection solution can safeguard your assets and grant you peace of mind.
Understanding the Issue: Ransomware Attacks in Kubernetes
A. Defining and Categorizing Ransomware
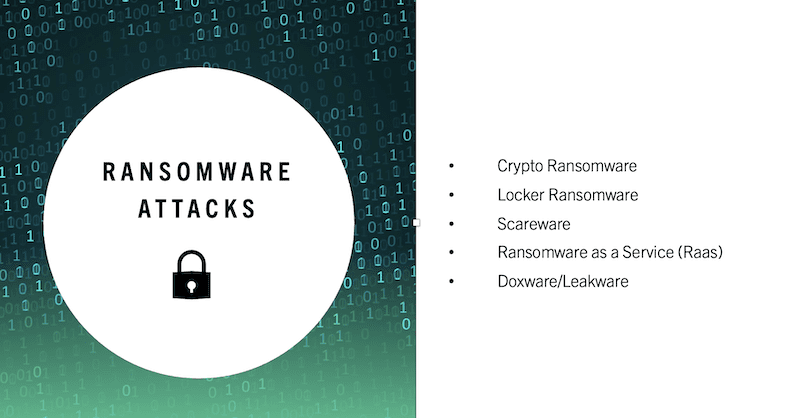
Ransomware refers to a software that locks or encrypts files and systems until a ransom is paid. There are types of ransomware which include:
- Encryption based ransomware: This variant encrypts files on the victim’s system making them inaccessible until a decryption key is obtained.
- Locker ransomware: Locker ransomware prevents victims from accessing their system effectively blocking their ability to open files or use applications.
- Scareware: Scareware displays warnings and notifications falsely claiming that the victim’s system is infected with malware. It deceives users into paying a ransom to eliminate these alleged threats.
B. Common Methods of Attack in Kubernetes
Ransomware attacks within Kubernetes exploit vulnerabilities and misconfigurations. Some prevalent attack methods include:
- Exploiting vulnerabilities in container images: Attackers can take advantage of security weaknesses in container images gaining access to the Kubernetes environment.
- Leveraging misconfigurations within Kubernetes clusters: configured or improperly set up Kubernetes clusters create opportunities for ransomware attacks. Attackers can exploit these misconfigurations to gain control over the system.
- Injecting code into container deployments: Attackers can insert code into container deployments enabling them to execute ransomware, within the Kubernetes environment.
C. The potential impact of attacks in Kubernetes is significant
Can result in various detrimental effects, such as:
- Loss or encryption of data: Attackers have the ability to encrypt or delete data within the Kubernetes system leading to the loss of information.
- Business disruptions and financial setbacks: If a ransomware attack compromises a Kubernetes environment it can cause disruptions resulting in downtime and financial losses for the organization.
- Damage to reputation: Ransomware attacks can tarnish an organization’s reputation, eroding trust among customers, partners and stakeholders.
Comparing Traditional Applications to Kubernetes and Trilio Ransomware: A Perspective
When it comes to protecting against ransomware it is important to understand the distinctions between applications and Kubernetes environments. Both have their risks and challenges. Kubernetes when combined with Trilio brings a unique perspective to the table.
There are differences between applications and Kubernetes in terms of the risks associated with ransomware and the measures taken for protection:
Traditional applications are typically hosted on single servers or small clusters which makes them more vulnerable to ransomware attacks. On the other hand Kubernetes distributes applications across a cluster of nodes providing resistance against such attacks. Additionally Kubernetes offers built in features for availability and disaster recovery that play a role in protecting against ransomware.
Trilio, a leading data protection solution for Kubernetes enhances its capabilities by offering point in time backups. This ensures that even if a ransomware attack occurs organizations can easily restore their applications to a state.
Using Kubernetes for application development and deployment comes with benefits. It enables scalability, flexibility and portability, across environments. However these advantages can also pose challenges when it comes to safeguarding against ransomware.
With the utilization of Kubernetes, where multiple containers and applications coexist within a cluster it becomes crucial to consider the impact of a compromised container, on others. This is because such an event could result in a broader scale attack. To safeguard the Kubernetes environment it becomes imperative to ensure containerization and segmentation.
Here’s how ransomware attacks can exploit the characteristics of Kubernetes environments:
Both traditional environments and those built on Kubernetes are susceptible to attacks. However Kubernetes introduces avenues for exploitation due to its distributed nature.
Attackers can take advantage of misconfigurations, unsecured APIs or vulnerabilities in third party components to gain access to the Kubernetes cluster. Inside they can leverage functionalities offered by Kubernetes, such as pod to pod communication or persistent storage features to propagate the ransomware throughout the environment.
To address these risks effectively Trilio provides monitoring of the Kubernetes environment. It promptly alerts administrators about any activities. Offers automated recovery options that restore data and applications back to a state free from ransomware threats.
Safeguarding Your Kubernetes Environment from Ransomware with Trilio
To ensure the safety of your Kubernetes environment, against attacks. Trillo is a tool that offers robust protection. With its features and capabilities Trillo provides a solution to help you mitigate the risks of ransomware and maintain smooth operations in your Kubernetes setup.
Here are some key measures to enhance security:
- Implementing Kubernetes RBAC (Role Based Access Control) enables grained access controls and restricts privileges.
- It’s essential to limit container permissions and capabilities to minimize the impact of attacks.
- Applying network policies helps isolate workloads and prevents the lateral movement of ransomware.
Effective vulnerability management plays a role:
- Regularly scanning container images and Kubernetes components for vulnerabilities helps identify security flaws.
- Keeping Kubernetes components and dependencies up to date with the security patches is important.
- Leveraging vulnerability management tools streamlines the process ensuring protection against emerging threats.
Adhering to practices for Kubernetes security is vital:
- Strengthening the host operating system running Kubernetes establishes a foundation for your environment.
- Enforcing authentication and encryption measures within Kubernetes clusters safeguards against access.
- Regularly auditing Kubernetes configurations ensures compliance with industry practices and security standards.
By following these guidelines you can significantly enhance your Kubernetes environment’s resilience against attacks while maintaining functionality.
Container Security, in Kubernetes:
- Implementing measures to create container runtime environments reducing the chances of ransomware infiltrating your containers.
- Utilizing tools for scanning images and protecting runtime to detect and prevent compromised containers from being deployed.
- Enforcing policies that enhance pod security to decrease the attack surface and restrict container actions.
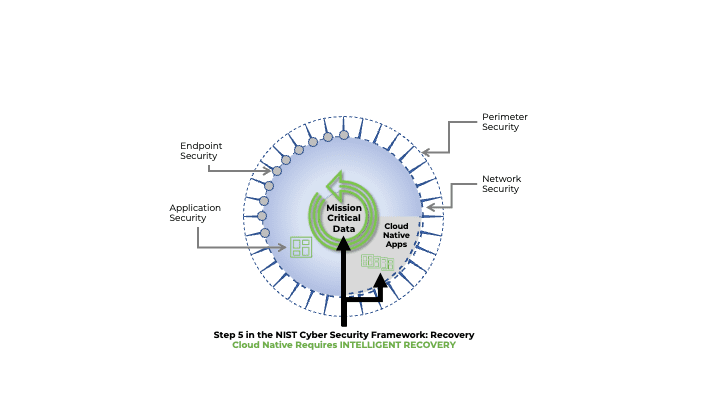
Backup and Disaster Recovery in Kubernetes:
- Implementing strategies to back up and restore data within the Kubernetes cluster ensuring business operations in case of an attack.
- Deploying disaster recovery solutions specifically designed for workloads to minimize the impact of incidents.
- Validating backup and recovery processes to ensure their reliability and effectiveness.
Security monitoring in Kubernetes:
- Implementing monitoring systems for analyzing logs enabling threat detection and prompt response to incidents.
- Leveraging security auditing tools native to Kubernetes for maintaining compliance with security standards.
- Utilizing anomaly detection techniques and behavior analysis methods proactively identify security risks. Mitigate them.
In conclusion
After delving into the realm of safeguarding Kubernetes environments from attacks and understanding the risks they pose it is evident that conventional applications and solutions fall short in mitigating these dangers. This is where Trilio emerges as a game changer providing protection for your Kubernetes environment.
Throughout this guide we have emphasized the significance of shielding your Kubernetes environment against attacks and how Trilio can assist you in achieving this objective. We have gained insights into the features and advantages of Trilio which include its ability to offer backup and recovery capabilities to ensure the availability and integrity of your data.
Moreover we have explored a range of tools and solutions for protecting Kubernetes environments from attacks with Trilio emerging as a prominent solution in this domain. By harnessing the power of Trilio you can proactively defend your Kubernetes environment against threats while safeguarding your business continuity.
To recap the takeaways
- Traditional applications and solutions are inadequate when it comes to safeguarding Kubernetes environments against attacks.
- Trilio provides protection against ransomware through its backup and recovery capabilities for your Kubernetes environment.
- Continuous monitoring, threat intelligence and staying informed about security advancements are crucial, for enhancing protection.
As technology continues to advance cybercriminals are also finding ways to carry out their attacks. To ensure the safety of your Kubernetes environment it is crucial to stay alert and adapt to emerging technologies and practices that enhance protection against ransomware.
One notable trend is the integration of intelligence and machine learning. These advanced technologies utilize algorithms and pattern recognition to detect and prevent threats, in real time increasing the security of your Kubernetes setup.
Another important practice involves implementing continuous data protection (CDP). This approach ensures that any changes made to your data are immediately recorded and stored, minimizing the risk of losing information in case of an attack.
Continuous monitoring, proactive threat intelligence gathering and staying up to date on security developments play roles in safeguarding against attacks. Cybercriminals are constantly evolving their techniques so taking an approach is essential. By monitoring your Kubernetes environment, keeping informed about the security updates and leveraging threat intelligence sources you can identify and mitigate potential threats before they cause significant harm.
Trilio stands at the forefront of defending Kubernetes environments against emerging threats by offering features and a proactive approach to protection.
By teaming up with Trilio and adopting these recommended approaches you can guarantee the protection, reliability and accessibility of your data while shielding your business against threats.